Instead of polling the API for changes, register an endpoint and Palm pushes events to you. Webhooks deliver events from all Palm products through a single integration — verification results, monitoring alerts, and compliance updates all arrive at the same endpoint.Documentation Index
Fetch the complete documentation index at: https://docs.getpalm.com/llms.txt
Use this file to discover all available pages before exploring further.
Setting up a webhook
When you create a webhook in Palm Console, you specify:- URL: The HTTPS endpoint that will receive events. HTTP is not supported.
- Events: The event types you want to subscribe to.
whsec_...) at creation time. This secret is returned once — store it securely. You’ll need it to verify that incoming requests are from Palm.
Event format
All events follow a consistent naming pattern:{resource}.{action}{resource}.{sub_resource}.{action}
| Field | Description |
|---|---|
id | Unique event identifier. Use for idempotency. |
object | Always event. |
type | The event type (e.g., user.verification.completed). |
created_at | ISO 8601 timestamp. |
data | Event-specific payload. Structure depends on event type. |
Event catalog
A note on naming: Webhook event types use
user (e.g., user.verification.completed) while the rest of the docs refer to “person” for KYC verification. These are the same entity — the event names reflect the API resource name.Verification events
Fired when verification processing completes. Payloads include the verification ID, risk level, match results, and — for business verification — associate results.| Event | Description |
|---|---|
user.verification.completed | Person (KYC) verification finished. |
business.verification.completed | Business (KYB) verification finished. Includes associate-level results. |
Monitoring events
Fired by the monitoring system when Palm detects changes from external sources (Secretary of State filings). These events only fire for businesses enrolled in Monitor.| Event | Description |
|---|---|
business.registration.updated | Registration data changed (status, name, address, officers, filings). Includes structured diffs with previous and current values. |
business.filing.due | A compliance filing deadline is approaching. |
business.filing.overdue | A compliance filing deadline has passed. |
Platform events
Fired when entities are created or removed through the API.| Event | Description |
|---|---|
user.created | A person was created. |
user.removed | A person was removed. |
business.created | A business was created. |
business.removed | A business was removed. |
session.completed | An onboarding session workflow completed. |
Example payloads
Verification completed
When a business verification completes, the payload includes risk assessment and field-level match results for the business and each associate:JSON
Registration change (monitoring)
When registration data changes, the payload includes structured diffs so you can process changes programmatically:JSON
data.business object is a lightweight reference — enough to identify which business changed. Use GET /business/{id} to retrieve the full record.
Filing deadline (monitoring)
Filing events include the filing type and due date:JSON
Verifying signatures
All webhook payloads are signed using HMAC-SHA256. Always verify signatures before processing events. Palm sends three headers with every delivery:| Header | Description |
|---|---|
Palm-Signature | Format: t={timestamp},v1={signature} |
Palm-Webhook-Id | The webhook endpoint receiving the event. |
Palm-Event-Type | The event type being delivered. |
- Extract the timestamp (
t) and signature (v1) from thePalm-Signatureheader. - Check the timestamp is within 5 minutes of current time. Reject stale timestamps to prevent replay attacks.
- Construct the signed payload:
{timestamp}.{raw_request_body} - Compute HMAC-SHA256 using your webhook secret (
whsec_...). - Compare your computed signature with the
v1value using constant-time comparison.
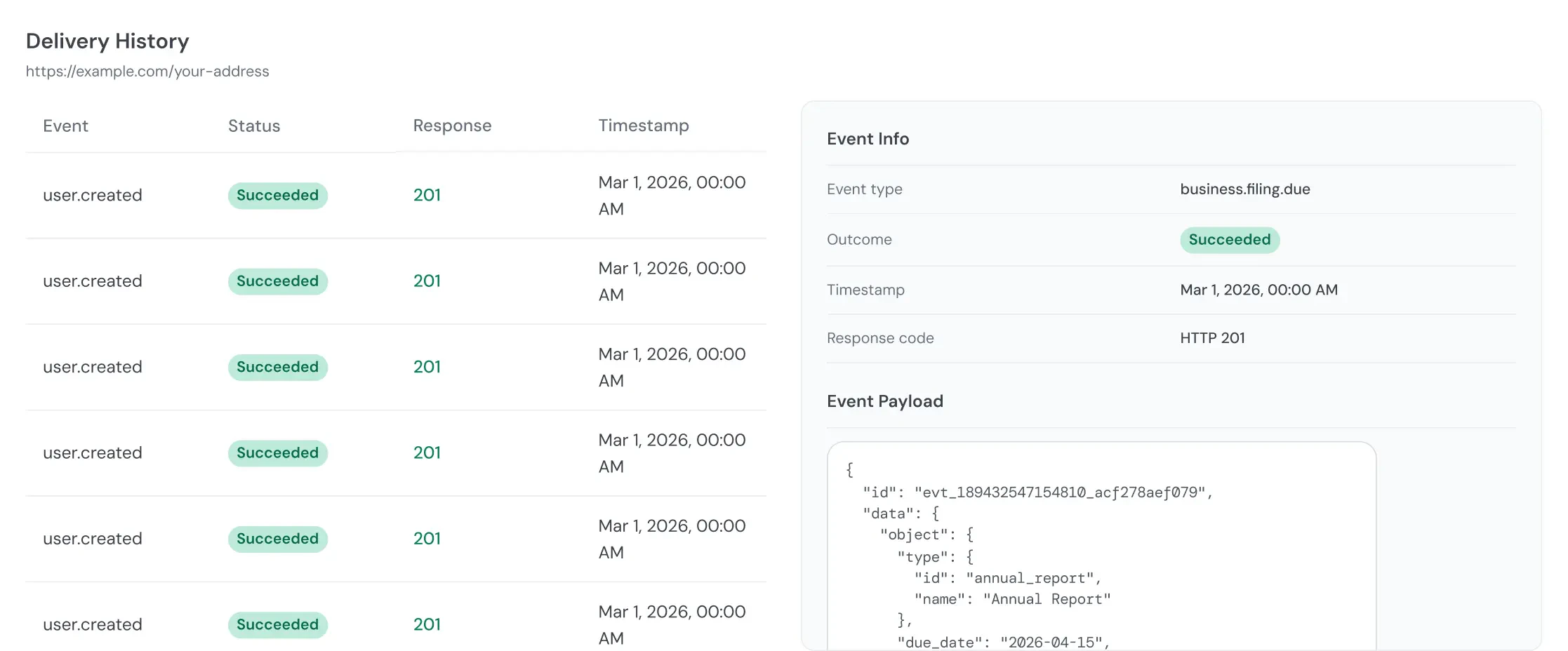
Retries and delivery
Timeout: Your endpoint must respond within 10 seconds. Return a 2xx immediately, then process the event asynchronously. Update event types: If your endpoint returns a non-2xx status or times out, Palm retries:| Attempt | Delay |
|---|---|
| 1st retry | 1 minute |
| 2nd retry | 5 minutes |
| 3rd retry | 30 minutes |
| 4th retry | 2 hours |
Idempotency
Events may be delivered more than once. Use the eventid field to deduplicate. If your processing is not naturally idempotent, store processed event IDs and skip duplicates.
Best practices
- Respond fast, process later: Return a 2xx immediately and handle the event asynchronously. Heavy processing that exceeds the 10-second timeout will trigger retries and eventually disable your webhook.
- Always verify signatures: Validate the
Palm-Signatureheader on every request. This is your only guarantee the event came from Palm. - Deduplicate with event IDs: Network issues can cause duplicate deliveries. Store the
idfrom each processed event to avoid processing it twice. - Subscribe selectively: Only subscribe to events you act on. If you don’t need
user.createdevents, don’t subscribe — it reduces noise and load on your endpoint. - Monitor delivery health: Check webhook execution logs in Palm Console regularly. A pattern of failures usually means your endpoint is slow or returning errors.

